Easy Setup
From zero to
continuous scanning
in four steps.
Setting up Datashielder takes roughly five minutes. Give us a root domain, we handle the reconnaissance, you choose what becomes a target. No source code, no integrations, no tickets.
At a glance
~5 minutes
A root domain
Zero
Within 24 hours
The setup flow.
Four short steps. Each one takes under a minute. You can walk away at any point — we save as you go.
- 01Organization
Create your organization.
All domains, targets, and reports live inside an organization. Invite teammates later from the dashboard — everyone on your team sees the same scans.
~30 seconds · single sign-on ready
- 02Target Set
Name a target set.
A target set is a named batch of domains scanned together — for example 'Production Endpoints' or 'Q1 Audit Scope'. Group anything you'd want in the same report.
One name, one line
- 03Domains
Add your root domains.
Type a root domain like example.com. We run subdomain enumeration in the background and surface everything we find — api, admin, staging, the forgotten 2019 microsite.
Automatic subdomain discovery
- 04Launch
Review, authorize, launch.
Tick the subdomains you want scanned, confirm you have authorization to probe them, and click create. Your first scan begins immediately.
First findings within 24 hours
The actual interface.
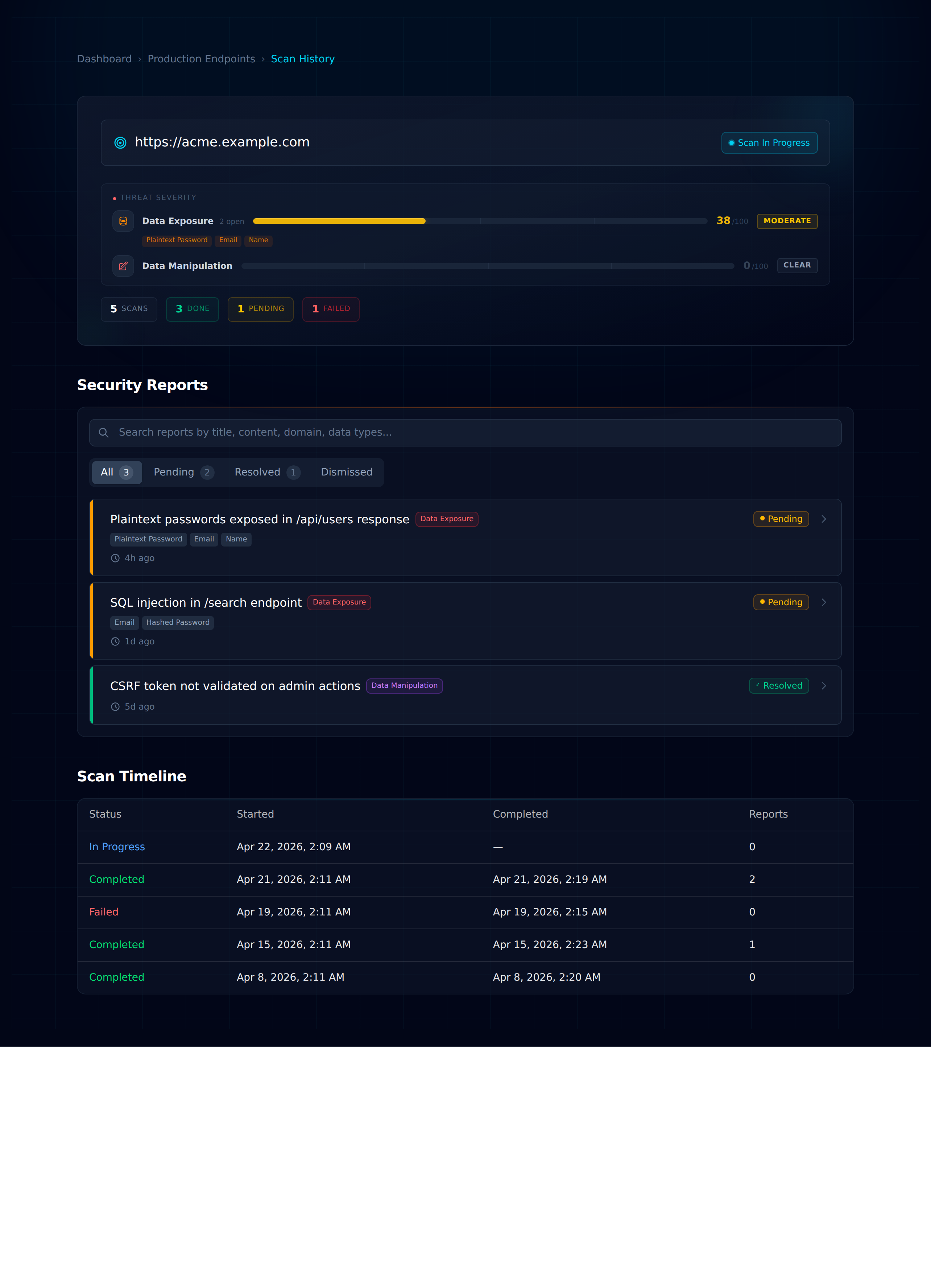
Not a mockup — these are real screens from the product. Every monitored target gets its own command centre with severity scoring, a full scan timeline, and a triage-ready report feed.
Every domain gets its own command centre.
Domain status, threat severity, scan timeline, and triaged findings on a single screen.
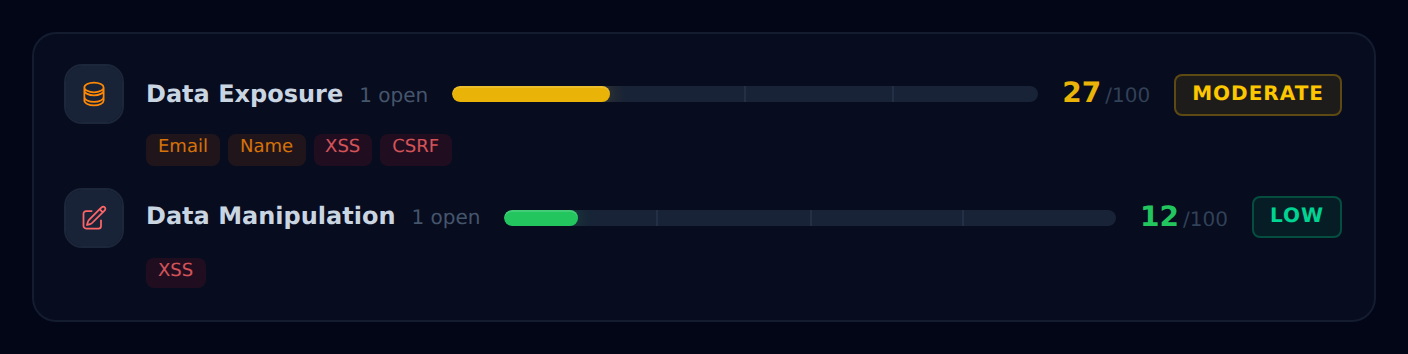
Risk, at a glance.
Each detector category gets a 0-100 score and colour-coded severity. Quick to read, quick to prioritise.
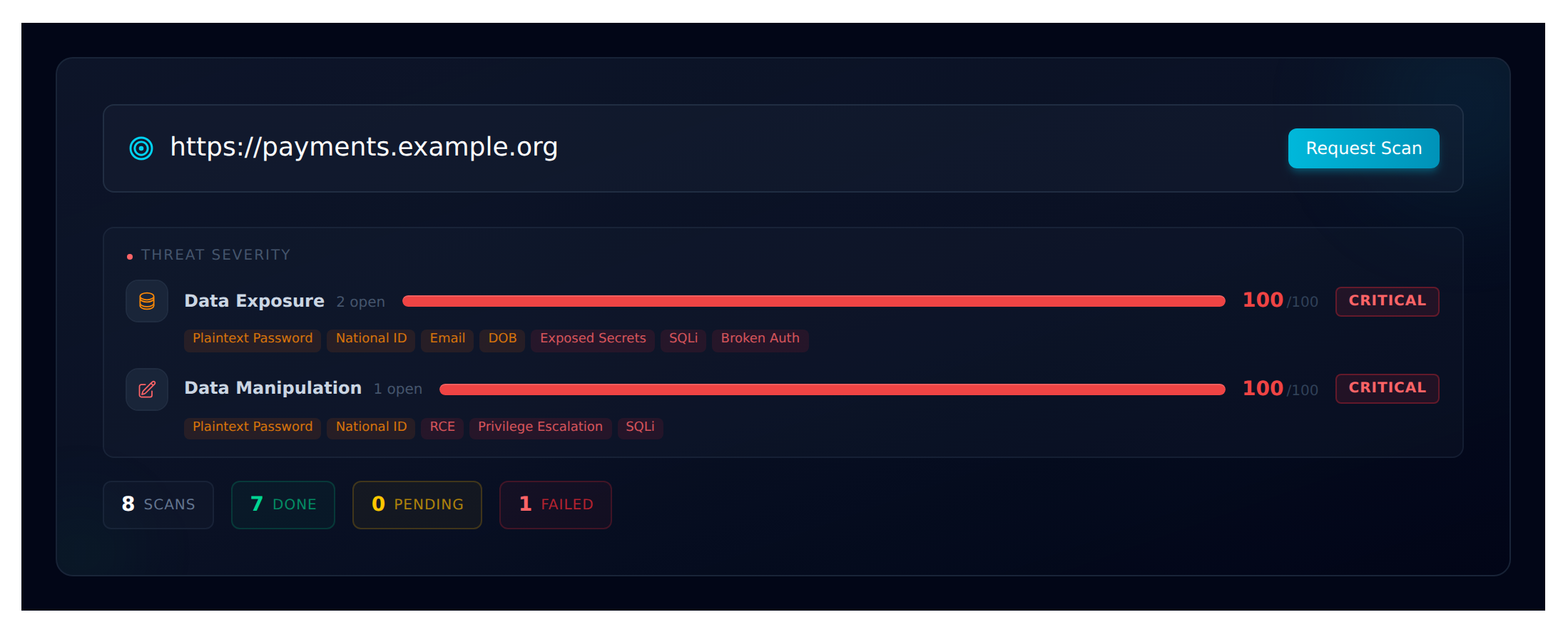
Monitored host, at a glance.
URL, last scan state, pending count, and severity for every detector — in one header strip.
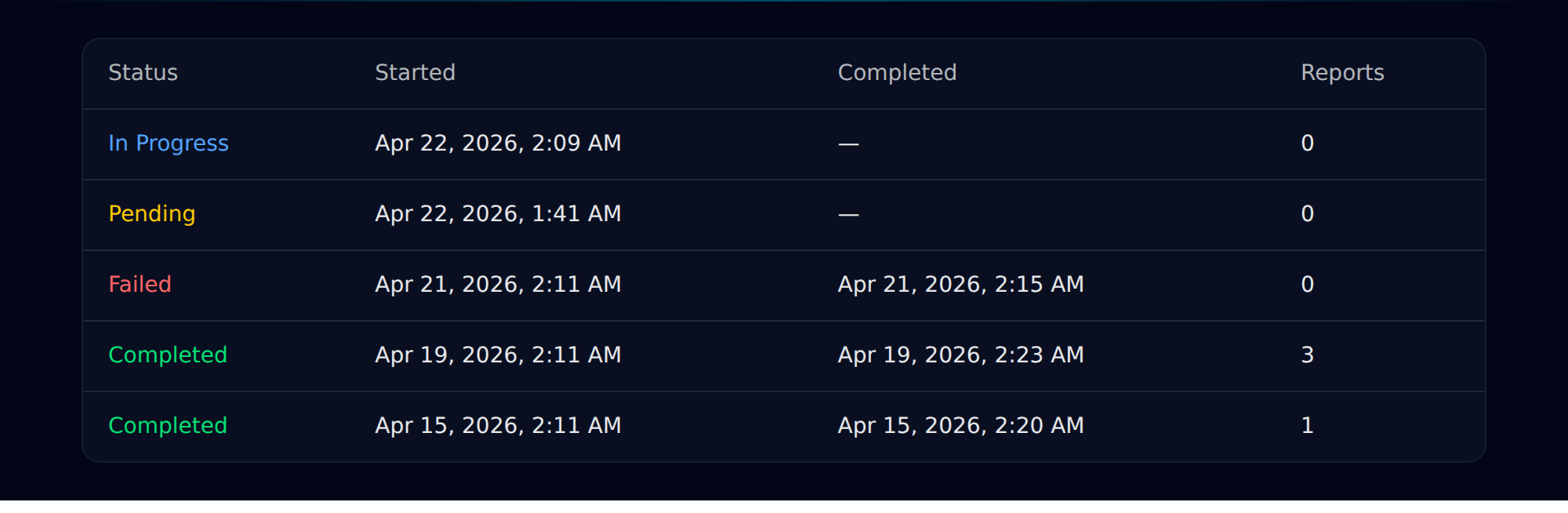
A clean audit trail.
Every scan is recorded — in progress, completed, failed — with exact start and finish timestamps.
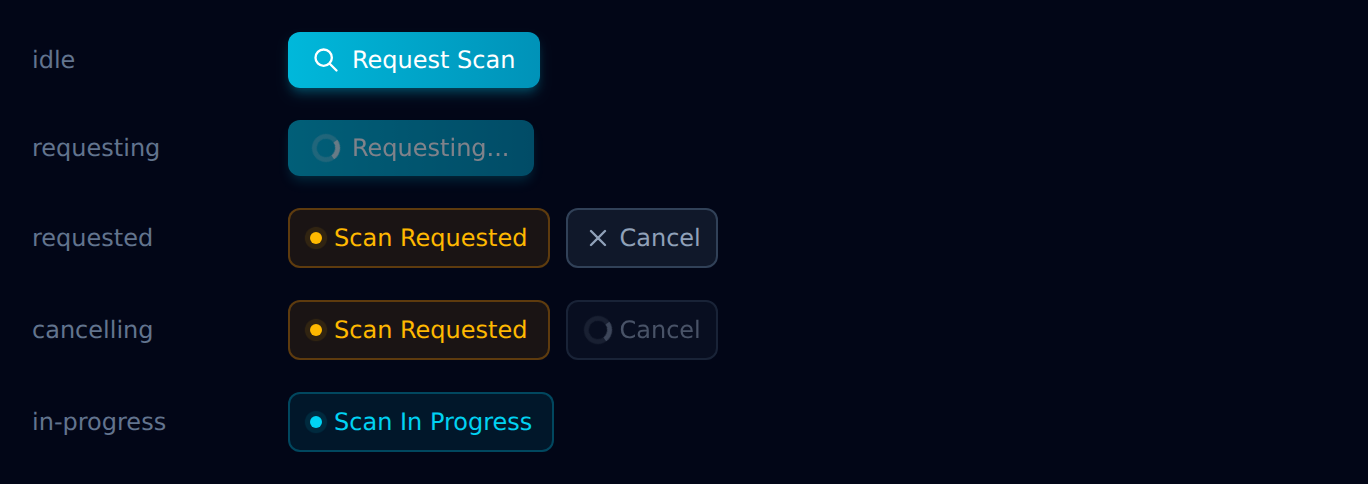
Scan on demand.
Kick off an ad-hoc scan between scheduled runs. Every state of the button is reachable in one place.
Every finding, triaged.
Pending, resolved, or dismissed — filter by state, category, or domain. Built to be worked through, not stared at.

Ready when you are
Five minutes to your first scan.
No engineering effort, no source-code access. Just a domain and a name — we'll take it from there.